

Then what you bought is not a mouse, it’s a proprietary peripheral that emulates a mouse when you install its propretary drivers.


Then what you bought is not a mouse, it’s a proprietary peripheral that emulates a mouse when you install its propretary drivers.


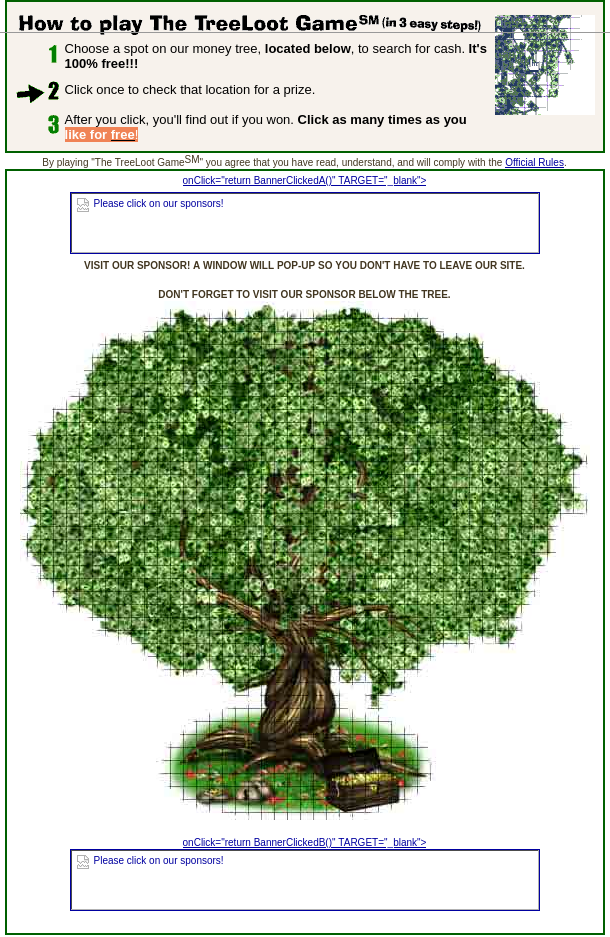
You clicked the tree somewhere and it would tell you either to try again, or you would win something. I think most people who won got $5 and a monkey plush toy. I’m not sure anyone ever won the jackpot. You could just click over and over again trying to remember where you had previously clicked, like a treasure hunt. Meanwhile they’re showing banner ads on the page.
It worked using the ismap attribute on the image which tells the browser to add the x,y coordinates of the user’s click to the link when fetching the result.


Does anyone remember the TreeLoot.com MoneyTree? It existed from 1998-2004 and looked like this:
I’m all in favor of going back to the old internet, but… not this.

Isn’t it the Cloudflare bot detection page that says “Just a moment” (… while we check that you’re human)?
It’s probably because lemmy servers are constantly loading a bunch of websites to generate previews and Cloudflare decides that those clients look like bots.


I read the source code and this is a hobby-project that you could write in an afternoon with no knowledge of cryptographic protocols.
There are dozens of obvious deficiencies even to me and I am no expert in cryptography. An easy example to point out is that there is no input validation and no error checking or exception handling. Both the client and server just assume that the other side is a well-behaving correct implementation.
The author should not be posting this around as if it’s a serious tool for people to use. If anything it’s a starting point for OP to get advice from experts on how real systems do this properly. I’d recommend that the author spends a LOT of time reading before doing. There are numerous design documents of real systems and protocols, and some good comprehensive books too.


Intel’s assets are worth more than Intel’s market cap. That’s how badly they’re doing in the stockmarket, and also shows you how market cap is a fairly irrelevant indicator of a company’s value.


Sorry, there’s no way Qualcomm is buying Intel as is
At the end of its third quarter of its fiscal 2024, […] Qualcomm had $7.8 billion in cash and […] just over $23 billion in total assets. That means Qualcomm, […] is almost certainly looking at a stock-for-stock transaction. As of writing, Qualcomm’s market cap is $188 billion, just more than double that of Intel’s at $93 billion.
In fact, Chipzilla may not be worth much to Qualcomm unless it can renegotiate the x86/x86-64 cross-licensing patent agreement between Intel and AMD, which dates back to 2009. That agreement is terminated if a change in control happens at either Intel or AMD.
While a number of the patents expired in 2021, it’s our understanding that agreement is still in force and Qualcomm would be subject to change of control rules. In other words, Qualcomm wouldn’t be able to produce Intel-designed x86-64 chips unless AMD gave the green light.
The amount of advertising for this tool in recent times is starting to look a lot like astroturfing.
Not my post btw, just sharing the link :)
Sorry for the reddit link, I don’t know of a mirror. This was posted just today, running on an EeePC:


The binaries in question are various GNU and FOSS tools from elsewhere, not part of the Ventoy project itself. So no, the Ventoy author does not own the copyright of the tools in question.


So your approach to security is that you cross your fingers and hope?


Ventoy has a lot of work to do if they want to earn our trust:
Remove BLOBs from the source tree #2795
This ticket has been open now for 5 months with no engagement from the maintainer.
Your install media and anything that modifies your EFI partition or UEFI firmware settings needs to be the most trusted part of your system. And here is Ventoy, a tool that looks open source and then includes a large number of binary blobs in its repository, with no indication of how they were compiled. This is horrible security practice and for me that’s enough for me to never use it.
You can also see a discussion on the subject on HN here: https://news.ycombinator.com/item?id=40689629
A much better alternative, if you want a multi-boot USB, is GLIM: https://github.com/thias/glim
It’s just a collection of Grub configs, so very simple and easy to audit.


You can’t improve on perfection.


I used Ubuntu from version 8.04 to 18.04 and not once did I have a successful upgrade between major versions. There is always something that gets broken to the point that a reinstall is necessary.


they can’t be jammed the way radio can.
I wonder how well these satellite laser links do with various types of cloud cover.
https://support.mozilla.org/en-US/kb/back-and-restore-information-firefox-profiles